
Release 90.4: Bulk Actions, Performance Tuning, and Community Enhancements

Release Info
Kpow can be found on Dockerhub
docker pull factorhouse/kpow-ee:90.4View our Docker quick start guide for help getting started.
Kpow can be found on ArtifactHub
Helm version: 1.0.43
helm repo add kpow https://charts.kpow.io
helm repo update
helm install --namespace factorhouse --create-namespace my-kpow kpow/kpow --version 1.0.43 \
--set env.LICENSE_ID="00000000-0000-0000-0000-000000000001" \
--set env.LICENSE_CODE="KPOW_CREDIT" \
--set env.LICENSEE="Your Corp\, Inc." \
--set env.LICENSE_EXPIRY="2024-01-01" \
--set env.LICENSE_SIGNATURE="638......A51" \
--set env.BOOTSTRAP="127.0.0.1:9092\,127.0.0.1:9093\,127.0.0.1:9094" \
--set env.SECURITY_PROTOCOL="SASL_PLAINTEXT" \
--set env.SASL_MECHANISM="PLAIN" \
--set env.SASL_JAAS_CONFIG="org.apache.kafka.common.security.plain.PlainLoginModule required username=\"user\" password=\"secret\";"
--set env.LICENSE_CREDITS="7"View our Helm instructions for help getting started.
Kpow can be found on the AWS Marketplace
View our AWS Marketplace documentation for help getting started.
Kpow can be downloaded and installed as a Java JAR file. This JAR is compatible with Java versions 11+.
View our JAR quick start guide for help getting started.
Kpow can be downloaded and installed as a Java JAR file. This JAR is compatible with Java 8.
View our JAR quick start guide for help getting started.
For more information, read the Kpow accessibility documentation.
Kpow v90.4 introduces a new Bulk Actions feature that allows you to take action on multiple resources in one click.
This release also resolves performance issues related to materialization and internal scheduled tasks, freshens up our UI with new icons, fixes a long-standing Jetty JAAS expired-session login bug, open-sources a couple of cool Clojure libraries, and bundles a number of smaller fixes and improvements.
Thanks to all our users who raised issues or requested features that are highlighted in this release. We hope you all have a restful holiday period and we'll see you in 2023!
Bulk Actions
Bulk actions allow a user to invoke a single mutation against multiple resources.
This can be particularly useful for tasks such as deleting large numbers of items in one go, like the example of deleting 300 topics in a single request.
See the Bulk Actions documentation for a guide to configuring permissions for your users, and an explanation of how Bulk Action processing works.
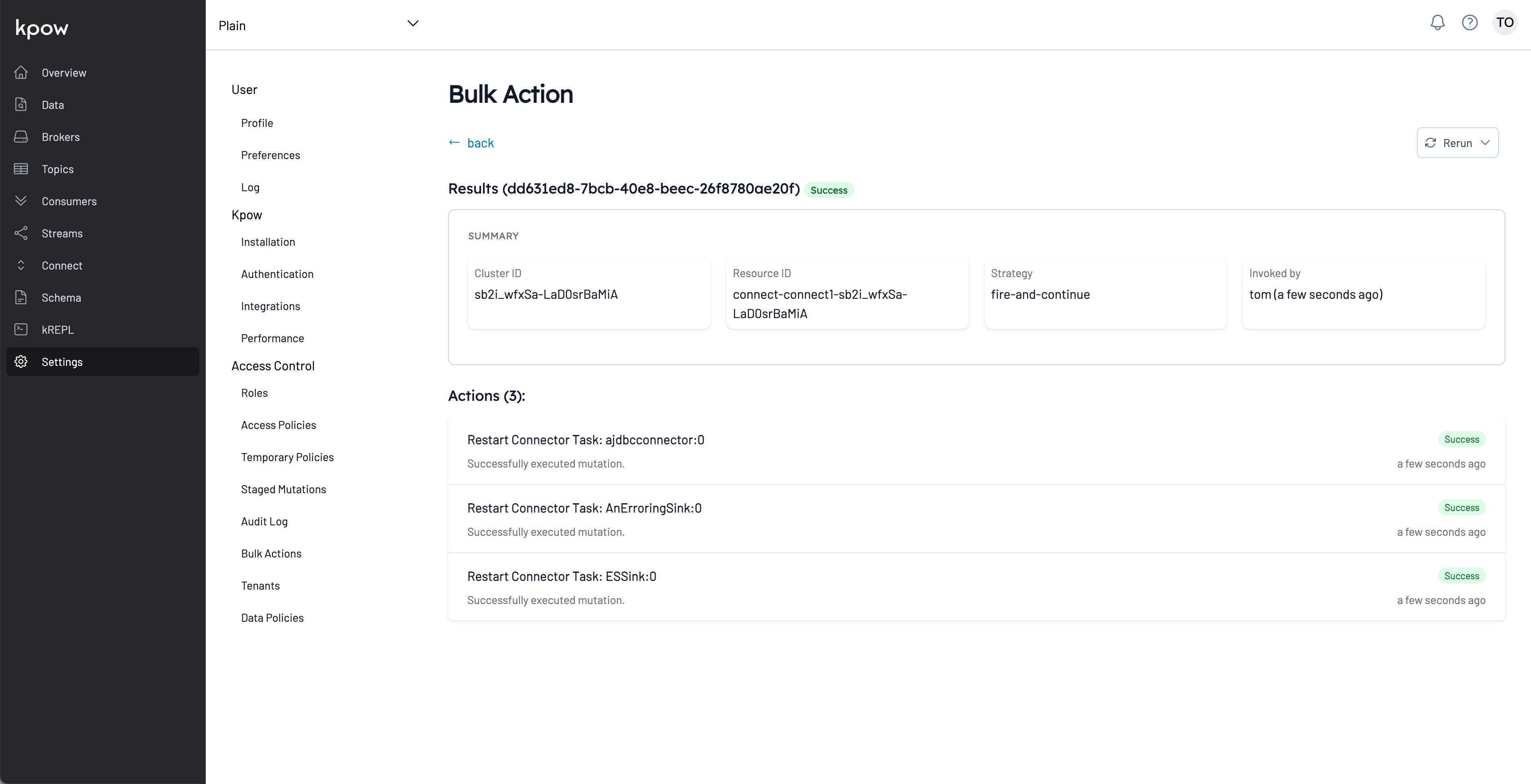
In a future release we will expand on this feature, allowing mixed and scheduled bulk actions.
Eventually this function will be available programtically via an API for CI/CD and other purposes.
This feature is not available in the Community Edition of Kpow.
Materialization and Scheduling Performance Improvements
We recently received a performance report from a customer with the following installation and our Helm chart resource defaults (1CPU / 4GB heap)
- Single Kpow Installation
- 12 Kafka Clusters
- 6 Connect Clusters
- 6 Schema Registries
With their assistance we were able to isolate a bug in our internal scheduled task manager responsible for performing observation and materialization of the data we use to provide the Kpow UI. We also improved the performance of materialization by about 50%, significantly dropping CPU resource requirements.
Accompanying these improvements we have adjusted the default Helm resource requests to 2 CPU and 8 GB heap. Those defaults now represent the upper limit we expect you might need when running Kpow with 12 Cluster, 12 Connect, 12 Schema.
You should experiment and adjust your memory and CPU allocation, as it is likely for single cluster installs you may use significantly less than those defaults.
Authentication Improvements
We have been working over the previous months to open-source the Clojure network layer that we use to interact with Jetty (the Java networking framework).
That work is now complete and Slipway is available in Github and Clojars, as is Kpow Secure.
As a part of that work we updated our Jetty dependencies to latest, squashed a long-standing bug where a user might observe an internal error page when re-authenticating an expired session, and introduced the ability to secure your 'javax.net.ssl.trustStorePassword' when specifying custom SSL certificates to use with LDAPS.
Using Kpow Secure with trustStorePassword
Use the standard approach for encrypting configuration, see our secure-config guide for full details.
Example configuration with encrypted javax.net.ssl.trustStorePassword:
Example configuration with encrypted javax.net.ssl.trustStorePassword:
java -Djava.security.auth.login.config=dev-resources/jaas/ldaps-jaas.conf \
-Djavax.net.ssl.trustStore=dev-resources/jaas/ldaps/local-client.jks \
-Djavax.net.ssl.trustStoreType=JKS
-Djavax.net.ssl.trustStorePassword=AES:ARClD4Hz3A2VpdCGqZArl/OglnIawMHRzW0cVjraODxIeg== \
-jar -Xmx4G ./kpow.jarUX Improvements
We have removed the 'Multiple Kpow Detected' warning page and replaced it with a notification that appears in the top-right alerts.
This release also bumps Kpow's icon set up to HeroIcons v2.0 - we think they look great!
Community Improvements
The community edition wizard has been improved to support configuration of MSK Connect (along with existin support for Confluent/Kafka Connect).
As always you can simply run CE from environment variables if you prefer, see our Community Edition docs for more.
Release v90.4 Changelog
See the Factor House Product Roadmap to understand current delivery priorities.
Kpow v90.4 Changelog
See the full Kpow Changelog for information on previous releases
- Introduce Bulk Actions for topic delete, group delete, schema edit, connector restart, pause, delete
- Improve snapshot materialization performance
- Improve healthcheck performance
- Improve 'multiple-instances detected' UX
- Improve UI with new Heroicons v2.0
- Improve audit log UI with pagination
- Improve community edition wizard with support for MSK Connect along with Confluent Connect and vanilla Kafka Connect
- Improve community edition with in-UI callouts to upgrade path
- Fix scheduler task contention issue
- Fix jetty authentication expired session re-login bug
- Fix connect bug where connectors with no tasks would not show in tables
- Support Kpow-Secure encryption of 'javax.net.ssl.trustStorePassword'
- Update Helm charts to 2CPU / 8GB heap as default
- Open-source Slipway and publish to Clojars
- Open-source Kpow Secure and publish to Clojars
- Add robots.txt with "User-agent: * Disallow: /"
.png)
Release 95.5: UI performance improvements
95.5 is a minor bugfix release focusing on UI performance and resolving some regressions introduced by Kpow 95.4.
Release 95.4: Concurrent data inspect, Strimzi support, and consumer group improvements
Kpow 95.4 introduces concurrent data inspect queries, Strimzi support, and improved consumer group management and monitoring.

Release 95.3: Memory leak fix for in-memory compute users
95.3 fixes a memory leak in our in-memory compute implementation, reported by our customers.
Start your streaming transformation today.
Try both Kpow or Flex free for 30 days with a single license - no credit card required.
